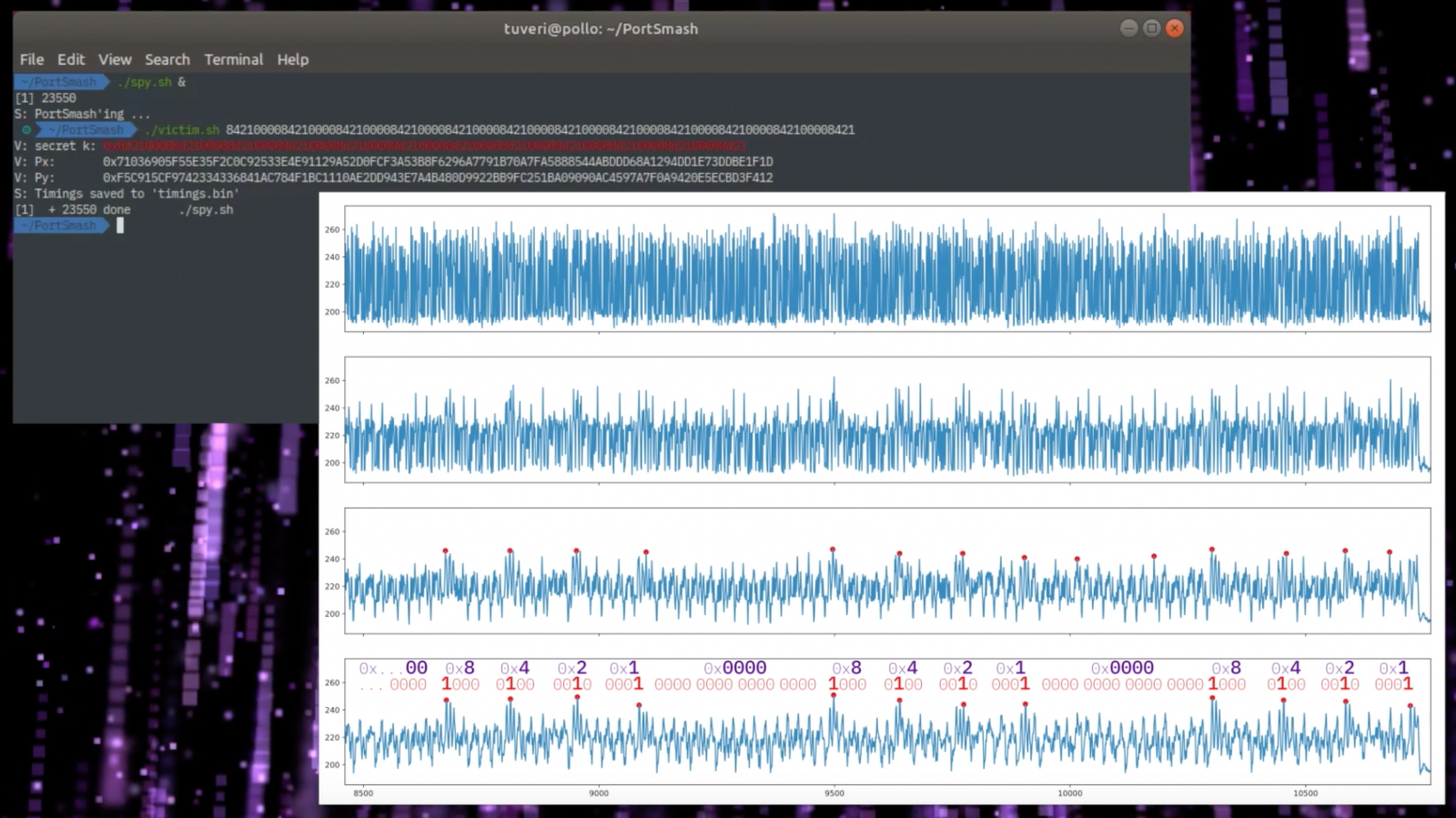
Title: Port Contention for Fun and Profit
Authors: Alejandro Cabrera Aldaya and Billy Bob Brumley and Sohaib ul Hassan and Cesar Pereida García and Nicola Tuveri
Venue: 40th IEEE Symposium on Security and Privacy, S&P 2019 (Oakland), San Francisco, CA, USA, May 20-22, 2019
https://twitter.com/campuscodi/status/1058333037543473152
New PortSmash Hyper-Threading CPU Vuln Can Steal Decryption Keys – by @LawrenceAbramshttps://t.co/Z9DQJcWcQR
— BleepingComputer (@BleepinComputer) November 3, 2018
PortSmash, as the latest attack targeting our processors is being called, exploits a largely overlooked side-channel in Intel’s hyperthreading technology. https://t.co/5RlhZBzsuJ
— Ars Technica (@arstechnica) November 5, 2018
https://twitter.com/marcan42/status/1058404388794847232