SAFEHORIZON

Crime-as-a-Service (CaaS) represents a troubling evolution in the cyber threat landscape, transforming criminal activity into a highly organized and commercialized enterprise. SAFEHORIZON offers computer law enforcement agencies (LEAs), emergency response teams (CERTs), and computer security incident response teams (CSIRTs) a toolbox with underdevelopment and improved open-source solutions that will be simple to plug-and-play, maintain, and adapt.
SAFEHORIZON aims to combat Crime-as-a-Service (CaaS) by leveraging intelligence from the clear, deep, and dark web, public dumps, and law enforcement datasets, combined with machine learning to extract actionable evidence for legal use. The project will deliver a user-friendly toolkit of interoperable tools, a monitoring platform for integrating these tools’ outputs, and a correlation engine to analyze large datasets. Additionally, SAFEHORIZON will provide datasets and notebooks to EU law enforcement and vetted organizations for easier data processing. The initiative also plans to disrupt cybercriminal networks by spreading disinformation to undermine their trust structures.
- Full Title: Innovations in Detecting and Disrupting Crime-as-a-Service Operations
- Duration & Grant: Research funding for 3 years (€4 million, 13 Partners)
- Project Type: HORIZON Research Innovation Action (Grant 101168562)
- Status: Active
- Contact: Juha Nurmi
QUBIP (HORIZON)
The exciting frontiers opened by the development of quantum computers (QC) come at the cost of breaking the foundations of current digital security. The research community is working to the definition of post-quantum cryptography (PQC) to counteract this threat. However, the transition to PQC is delicate and takes time because it impacts many functions, algorithms, and protocols in a-priori unknown cascade of dependencies.
QUBIP is conceived to contribute to the EU transition to PQC with the goal of simplifying and making replicable the process by means of recommended practices and counteract post-quantum threats as soon as possible. QUBIP focuses on digital infrastructure addressing the 5 main building blocks that use public-key cryptography for security purposes: hardware, cryptographic libraries, operating system, communication protocols, and applications.
QUBIP address all 5 blocks coherently solving all dependency issues that may arise inside each block and among blocks with the final aim to validate at TRL6 three infrastructures making use of those blocks in IoT-based Digital Manufacturing, Internet Browsing, and Software Networks Environments for Telcos use cases. The return-of-experience from the three practical exercises is then maximized by developing a migration playbook, that will contain the lessons learned and an evaluation of all the technical, economic, and legal barriers encountered together with the solutions to overcome them to enable the definition of a replicable process, suitable to provide structured accompanying and practical guidance to industrial stakeholders. The technical activities are corroborated by three supporting activities (i) evaluation of the capabilities of QCs to assess their implication to primitives, algorithms and protocols adopted, and contribution to (ii) standardization efforts addressing transition to PQC processes and (iii) policy measures addressing technology changes coming from the advent of QC and PQC.
- Full Title: Quantum-oriented Update to Browsers and Infrastructure for the PQ Transition (QUBIP)
- Duration & Grant: Research funding for 3 years (€5 million, 11 Partners)
- Website: https://qubip.eu
- Project Type: HORIZON Innovation Action (Grant 101119746)
- Status: Active
- Contact: Nicola Tuveri
HARPOCRATES (HORIZON)

Project HARPOCRATES, focuses on setting the foundations of digitally blind evaluation systems that will, by design, eliminate proxies such as geography, gender, race, and others and eventually have a tangible impact on building fairer, democratic and unbiased societies. To do so, we plan to design several practical cryptographic schemes (Functional Encryption and Hybrid Homomorphic Encryption) for analysing data in a privacy-preserving way.
Besides processing statistical data in a privacy-preserving way, we also aim to enable a richer, more balanced and comprehensive approach where data analytics and cryptography go hand in hand with a shift towards increased privacy.
- Full Title: Federated Data Sharing and Analysis for Social Utility (HARPOCRATES)
- Duration & Grant: Research funding for 4 years (4,408,800€, 13 Partners)
- Website: https://harpocrates-project.eu/
- Project Type: Research & Innovation (Grant 101069535)
- Status: Active
- Role: Coordinator
- Contact: Antonis Michalas
FACILIATE (H2020)

FACILITATE is a project built on a patient-centered, data-driven, technological platform where an innovative data sharing and re-use process allows the returning of clinical trial data to study participants within a GDPR compliant and approved ethical framework. FACILITATE starts-off by providing clear rules in a trusted ethical, legal and regulatory ecosystem before engaging patients as data generators. This avoids the current situation where clinical data are siloed in separate repositories without any possibility to be used beyond their original single-sided purpose. FACILITATE will provide the technological solutions to comply with GDPR in medical research by building on the empowered stakeholders’ willingness to share and re-use their data.
- Full Title: FrAmework for ClInicaL trIal participants daTA reutilization for a fully Transparent
and Ethical ecosystem (FACILITATE) - Duration & Grant: Research funding for 4 years (3,260,00€, 26 Partners)
- Website: https://facilitate-project.eu/
- Project Type: Research & Innovation (Grant 101034366)
- Status: Active
- Contact: Antonis Michalas
SPIRS (H2020)
SPIRS encompasses the complete design of a platform that integrates a hardware dedicated Root of Trust (RoT) and a processor core with the capability of offering a full suite of security services. The SPIRS platform will leverage this capability to support privacy-respectful attestation mechanisms and enable trusted communication channels across 5G infrastructures and other Industry 4.0 use cases. RoT is implemented in hardware with a dedicated circuitry to extract a unique digital identifier for the SPIRS platform during its entire lifetime. The project also features a Trusted Execution Environment (TEE), secure boot, and runtime integrity. Furthermore, resilience and privacy protection are major concerns in this project, and it endeavors to the design of a decentralized trust management framework to achieve adequate security and privacy tradeoffs.
- Full Title: Secure Platform for ICT Systems Rooted at the Silicon Manufacturing Process (SPIRS)
- Duration & Grant: Research funding for 3 years (€5 million, 9 Partners)
- Website: cordis.europa.eu
- Project Type: Research & Innovation (Grant 952622)
- Status: Active
- Contact: Alejandro Cabrera Aldaya, Billy Brumley
ARROWSMITH (CRA)

We will augment unmanned aerial vehicles (UAV) with SoC-based devices and technologies for hardware-based security, utilizing Trusted Execution Environment (TEE) technologies such as ARM TrustZone and RISC-V analogues. We are interested in their access control and Trusted Application (TA) features. We then build lightweight cryptographic protocols that will allow constrained devices (including UAVs, drones) to communicate securely over possibly insecure channels. Finally, we investigate ways of leveraging the power of secure hardware such as TEEs in order to design and develop protocols and TAs that will allow data processing (both in encrypted and unencrypted form) in a privacy-preserving manner.
- Full Title: Living (Securely) on the Edge — Designing Privacy-Preserving Smart Cities Using Cryptography and Machine Learning
- Duration & Grant: Research funding for 3 years (1,500,000 USD)
- Website: research.tuni.fi
- Project Type: Cybersecurity Research Award (CRA), Technology Innovation Institute (TII)
- Status: Active
- Contact: B. Brumley, A. Michalas, J. Kämäräinen, H. Edelman
KyLä (ESR)

KyLÄ responds to needs of SME companies in Pirkanmaa by deepening co-operation between the cyber security laboratories of the Tampere universities community (TAMK+TAU). The project builds a co-operation network of companies in the Pirkanmaa area and the Tampere universities community, plans and develops a controlled entity from the existing industrial cyber security related technical environments, and develops in laboratory environments towards innovation platform. The project will generate new activities in which the technical environments of educational institutions will open up as a unified platform for innovation and development suitable for SME use.
- Full Title: Kyberturvallisuuden Laboratoriot Älyteollisuudelle / Cyber Security Laboratories for Smart Industry
- Duration & Grant: Research funding for 2 years (385,000€)
- Website: projects.tuni.fi/kyla/
- Project Type: European Social Fund (ESR) Grant A76619
- Status: Active
- Contact: Marko Helenius
ASCLEPIOS (H2020)

The vision of ASCLEPIOS is to maximize and fortify the trust of users on cloud-based healthcare services by developing mechanisms for protecting both corporate and personal sensitive data. While researchers have developed many theoretical models that could enhance the security level of healthcare services, only a rudimentary set of techniques are currently in use. ASCLEPIOS is addressing these limitations by utilizing several modern cryptographic approaches to build a cloud-based eHealth framework that protects users’ privacy and prevents both internal and external attacks.
- Full Title: Advanced Secure Cloud Encrypted Platform for Internationally Orchestrated Solutions in Healthcare (ASCLEPIOS)
- Duration & Grant: Research funding for 3.5 years (4,840,000€, 10 Partners)
- Website: asclepios-project.eu
- Project Type: Research & Innovation (Grant 826093)
- Status: Completed (June 2022)
- Contact: Antonis Michalas
CYBELE (H2020)
CYBELE generates innovation and creates value in the domain of agri-food, and its verticals in the sub-domains of PA and PLF in specific, as demonstrated by the defined real-life industrial cases, empowering capacity building within the industrial and research community. Since agriculture is a high-volume business with low operational efficiency, CYBELE aspires at demonstrating how the convergence of HPC, Big Data, Cloud Computing, and the IoT can revolutionize farming, reduce scarcity and increase food supply, bringing social, economic, and environmental benefits. CYBELE intends to safeguard that stakeholders have integrated, unmediated access to a vast amount of large scale datasets of diverse types from a variety of sources, and they are capable of generating value and extracting insights, by providing secure and unmediated access to large-scale HPC infrastructures supporting data discovery, processing, combination and visualization services, solving challenges modeled as mathematical algorithms requiring high computing power.
- Full Title: Fostering Precision Agriculture and Livestock Farming Through Secure Access to Large-Scale HPC-Enabled Virtual Industrial Experimentation Environment Empowering Scalable Big Data Analytics (CYBELE)
- Duration & Grant: Research funding for 3.5 years (12,407,673€, 31 Partners)
- Website: cybele-project.eu
- Project Type: Research & Innovation (Grant 825355)
- Status: Completed (May 2022)
- Contact: Antonis Michalas
SCARE (ERC)

Side-channel analysis (SCA) is a cryptanalytic technique that targets not the formal description of a cryptographic primitive but the implementation of it. Examples of side-channels include power consumption, electro-magnetic radiation, acoustic emanations, and various timings. Attackers then use this auxiliary signal to recover critical algorithm state and, in combination with cryptanalytic techniques, secret key material. This is a young but very active field within security and cryptography stemming from covert channels. SCA is the focus of SCARE. Objectives include the discovery of next generation covert channels, paving the way for novel SCA classes, and extending these to full-fledged end-to-end SCA attacks by identifying specific vulnerabilities in widely-deployed cryptography software libraries such as OpenSSL and hardware-assisted security technologies such as Trusted Execution Environments (TEE). In turn, SCARE will deliver a methodology for SCA security assurance: not just development, evaluation, and deployment of acute countermeasures, but bringing SCA into the product life cycle as part of continuous integration.
- Full Title: Side-Channel Aware Engineering (SCARE)
- Duration & Grant: Research funding for 5 years (1,500,000€)
- Website: cordis.europa.eu
- Project Type: ERC Starting Grant 804476
- Status: Active
- Contact: Billy Brumley
KYBERTURVAAJA (ESR)
![]()
The main goal of KYBERTURVAAJA (CYBERKEEPER) is to prepare and offer security education for work life. This is based on already existing study modules and infrastucture. Participating companies are from each local region, focused on SME companies. The aim is to utilize the entire network of participating universities.
- Full Title: KYBERTURVAAJA
- Duration & Grant: Research funding for 2 years (650,000€, 5 Partners)
- Website: projects.tuni.fi/kyberturvaaja/
- Project Type: European Social Fund (ESR) Grant S21325
- Status: Completed July 2018
- Contact: Marko Helenius
D4Value (Business Finland)
 The D4Value program, co-ordinated by DIMECC, focuses on autonomous supply chain for maritime logistics as well as manufacturing’s cases. It attempts to disrupt supply chain ecosystems by featuring novel value creation and attractive value sharing through introducing ecosystem level business models and digital platforms that enable scalable, replicable, digitalized, and autonomous door to door supply chain processes. D4Value targets to a create the basis and strategies for business ecosystem formation around disrupting supply chain and thereby create new business models with promising value creation which motivates partners to join the ecosystem. In order to do so, D4Value will develop and test key technologies to develop the basis for open, scalable, secure, trusted and desirable platform, that enables a platform-based business in autonomous value chain.
The D4Value program, co-ordinated by DIMECC, focuses on autonomous supply chain for maritime logistics as well as manufacturing’s cases. It attempts to disrupt supply chain ecosystems by featuring novel value creation and attractive value sharing through introducing ecosystem level business models and digital platforms that enable scalable, replicable, digitalized, and autonomous door to door supply chain processes. D4Value targets to a create the basis and strategies for business ecosystem formation around disrupting supply chain and thereby create new business models with promising value creation which motivates partners to join the ecosystem. In order to do so, D4Value will develop and test key technologies to develop the basis for open, scalable, secure, trusted and desirable platform, that enables a platform-based business in autonomous value chain.
- Full Title: Design 4 Value
- Duration & Grant: Research funding for 2 years (€12 million, 20 Partners)
- Website: DIMECC D4Value
- Project Type: DIMECC Programme
- Status: Completed April 2019
- Contact: Bilhanan Silverajan
ACTIVE (EIT Digital)
 The ACTIVE programme aims at accelerating the creation of applications & services by providing a unified approach for developers and industry to support the widespread growth in IoT. ACTIVE addresses the Internet-of-Things market, which currently is in its early stages, and dominated by domain-specific platforms, proprietary architectures and vertically divided technology silos. ACTIVE enables crossing these divisions by offering a unified approach consisting of end-to-end components and solutions.
The ACTIVE programme aims at accelerating the creation of applications & services by providing a unified approach for developers and industry to support the widespread growth in IoT. ACTIVE addresses the Internet-of-Things market, which currently is in its early stages, and dominated by domain-specific platforms, proprietary architectures and vertically divided technology silos. ACTIVE enables crossing these divisions by offering a unified approach consisting of end-to-end components and solutions.
A special focus is set on connectivity, middleware, device management and privacy & security, which are provided as a set of Application Programming Interfaces (APIs).
- Full Title: Advanced Connectivity Platform for Vertical Segments
- Duration & Grant: Research funding for 3.5 years (€9 million, 14 Partners)
- Website: EIT Digital ACTIVE
- Project Type: High Impact Initiative
- Status: Completed December 2018
- Contact: Bilhanan Silverajan
ATHENA (Academy of Finland)
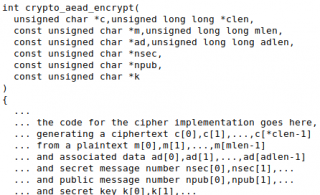
As opposed to a traditional block cipher that only provides confidentiality, Authenticated Encryption (AE) is a cryptographic primitive achieving confidentiality, integrity, and authenticity in a single function. AE is a fundamental concept in e.g. TLS, with several cipher suites utilizing AES Galois Counter Mode (GCM). Briefly, a TLS Cipher Suite is a combination of cryptographic algorithms to achieve a number of high level security goals. In ATHENA, we scrutinize one of those goals in particular: authentication. Furthermore, in the context of real-world systems and protocols, TLS being the focus and OpenSSL the most popular open source implementation.
- Full Title: Authenticated Encryption Analysis (ATHENA)
- Duration & Grant: Research funding for 2 years (241,746€)
- Website: pervasive.cs.tut.fi
- Project Type: Strategic Research Council 303814
- Status: Completed September 2018
- Contact: Billy Brumley
